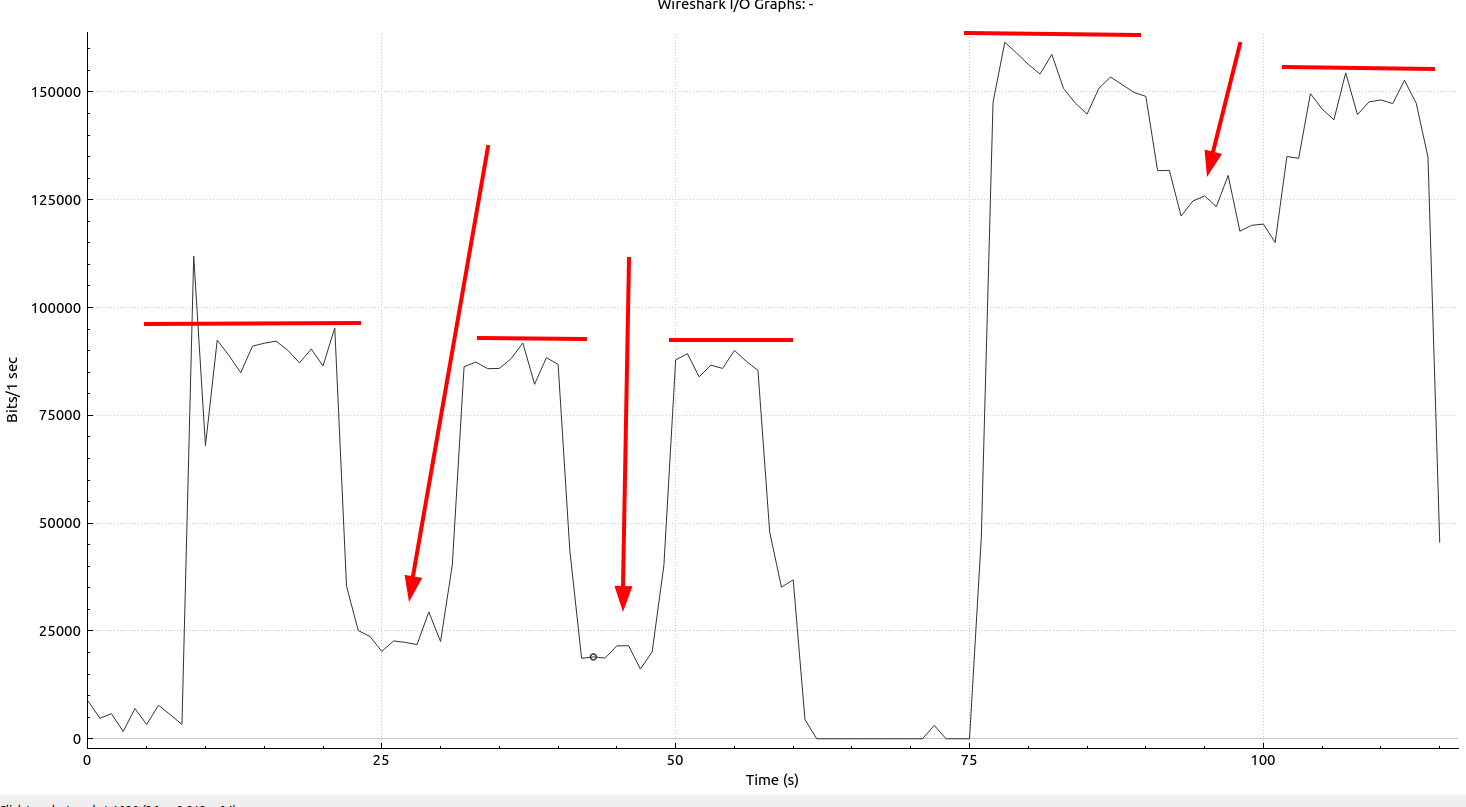
In my simple universe, I always thought that all apps using Android’s built-in WebRTC stack for voice and video calls would pretty much use the same parameters and hence, the encrypted data stream would pretty much look the same. It turns out, however, that this is not at all the case. This discovery made me go off on quite a bit of a tangent, and I decided to have a look at a number of different related things, including cellular network handover behavior and other things. But let’s start at the beginning, the use of WebRTC by different ‘Over the Top’ voice applications. Personally, I use two messengers: Signal and Conversation and it turns out they use WebRTC quite differently!
Continue reading Signal vs. Conversations – OTT Voice Observations – Part 1