
One VPN technology I wanted to try out for quite some time now is Wireguard. Everybody I talk to about the topic speaks very highly of it but unfortunately, the stable version was just released a bit too late for proper NetworkManager support to be included in Ubuntu 20.04 last year. While I could live with a couple of scripts to establish and tear down a tunnel to my home network, that’s unfortunately not an option for others I work with. But then I remembered that OpenWrt, the open source Linux operating system for embedded network devices such as Wi-Fi access points, has support for the protocol. And as I just needed to update a Linksys WRT-1200 AC Wi-Fi Router to the latest OpenWrt version anyway, I used the opportunity to gain some experience with the protocol along the way.
As I don’t have a Wireguard server at home so far, I decided to use a public VPN provider that has good Wireguard support and a step by step ‘howto’ to get Wireguard working with the Wi-Fi router. And indeed, getting Wireguard working on OpenWrt is not that difficult.
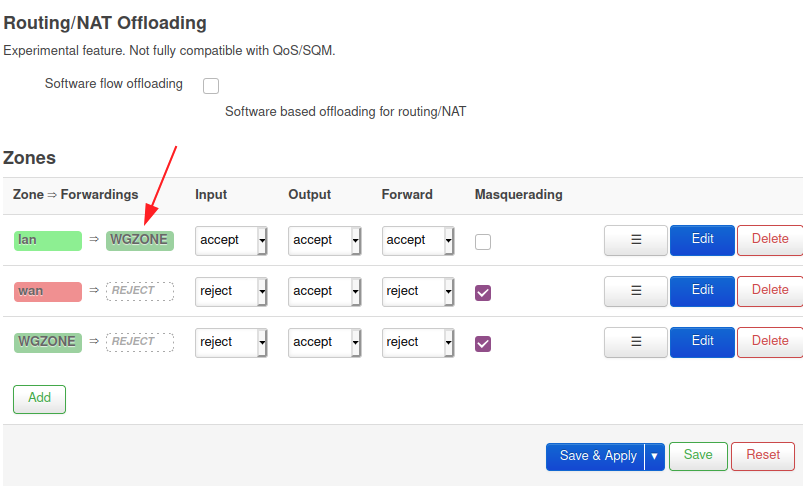
In essence, one downloads and installs the Wireguard packages over the OpenWrt GUI and then creates a new Wireguard tunnel interface. There are only a few parameters that need to be configured for this interface, the main ones being the public and private Wireguard keys that were generated by the VPN provider and the IP addresses for the tunnel endpoints. I won’t go into the details here, as the VPN provider of your choice should have a ‘howto’ for this. Once done, the Wi-Fi access point has a new interface that can be selected as backhaul interface instead of the plain WAN connection.
To see how stable the tunnel is in practice I connected my devices to the Wi-Fi of the Linksys router and ran my Internet connectivity over the tunnel for two days. I didn’t experience a single failure, despite working the connection quite hard and transferring at least 50 GB over it. Also resetting the router to see if the tunnel would come up automatically worked as advertised. No manual intervention necessary and no leakage over the plain WAN connection after the reboot before the tunnel was up again. O.k., I’m convinced, this is the VPN protocol I will go forward with!